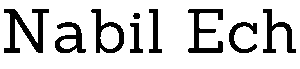
Why XOR Is a Terrible Way to Combine Hashes (And How It Cost Panoptic $4M in Risk)
There is a tempting idea in cryptographic design: take individual hash outputs and XOR them together. It is simple, fast, and incremental — if one input changes, you just XOR out the old hash and XOR in the new one. No need to recompute the whole thing. The problem is that XOR hashing is broken. […]
Why XOR Is a Terrible Way to Combine Hashes (And How It Cost Panoptic $4M in Risk) Read More »